HOWTO: Scan and Block Packages in ProGet
Configuring ProGet to automatically scan third-party open-source packages and container images for vulnerabilities is simple and straightforward.
This guide will explain how to scan and assess vulnerabilities, and how you can configure blocking rules and assessments when a package is found to be vulnerable.
Step 1: Enable Vulnerabilities Feed Feature
This step is enabled by default. Unless this feature is disabled on your instance, you can skip to step 2.
To configure vulnerability blocking on a feed, first navigate to the feed and click the "Feed Properties" tab.
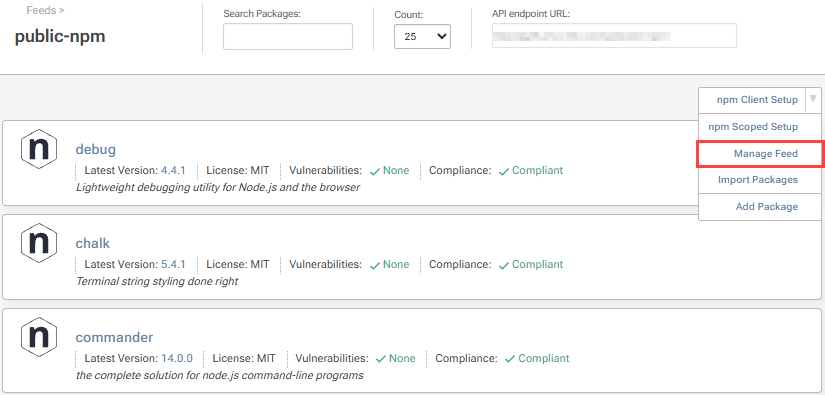
Then click "change" in the Feed Features section under "Other Settings".
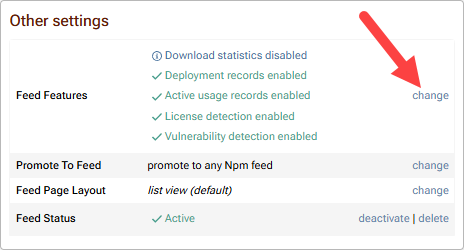
Enable "Display vulnerability information and enforce vulnerability compliance rules" and click "Save".
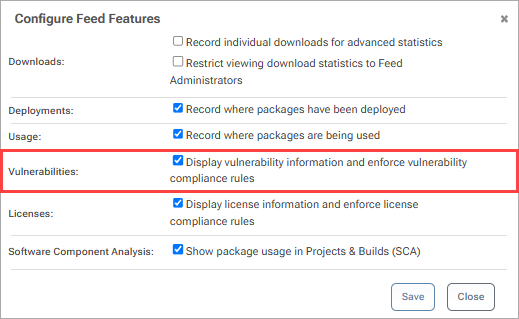
For container feeds such as Docker, you also need to make sure "Layer Scanning" is enabled. This is found under the container settings (e.g. "Docker Settings) when navigating to "Manage Feed" following the instructions above. As with the other settings in this step, this is enabled by default.
Step 2: Use Vulnerable Package
When packages are used in your Projects and Builds in ProGet, they will be auto assessed. You can view any identified vulnerabilities by navigating to "Reporting & SCA" and then selecting the Build.

From here, select the "Vulnerabilities" tab to view all identified vulnerabilities in the Build.

Step 3: Scan your Build
You can scan your Build using pgutil and the pgutil builds scan command. This will analyze the packages used in the build for any vulnerabilities.

Here we can see the a number of vulnerabilities have appeared in the scan, resulting in the affected package being assessed as Noncompliant. This will prevent the build from being deployed to the next stage.

Step 4: (Optional) Run an audit
You can also run pgutil builds audit right before deploying to production to identify any vulnerabilities that may have surfaced since you originally ran pgutil builds scan.

Step 5: (Optional) Block Noncompliant Packages
To prevent vulnerable packages from entering your development and being used in production to begin with, you can block noncompliant packages from being downloaded at the feed level.
Navigate to the feed and select "Policies and Blocking".

From here scroll to the bottom and select "Change Blocking Settings".

Then from "Feed Setting" select "Block noncompliant packagess" and select "Save".

This will prevent noncompliant packages from being downloaded.
Step 6: (Optional) Edit Package Policy Rules
Package compliance policies, available with paid ProGet, is configured on a feed-by-feed basis.
However, you can also set global compliance rules allowing you to block any package with unassessed vulnerabilities.
Navigate to "Administration Overview" and select "Package Policies & Rules" under "Global Components".
Then select "edit" on the right of "Global" policies.
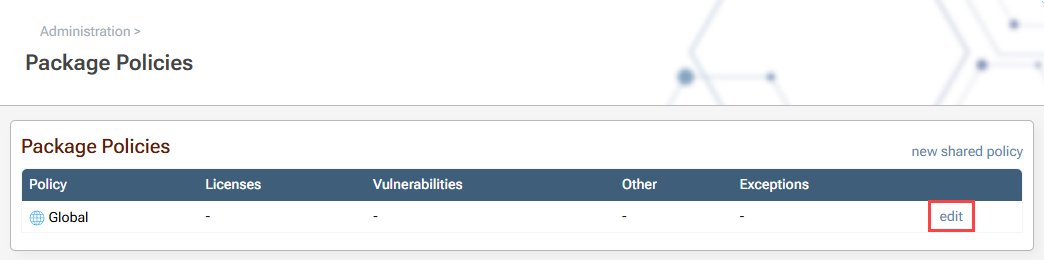
Under the "Vulnerabilities Rules" category, select "edit". Now select the "General" tab and under "Unassessed vulnerability" select "Noncompliant". Then select "Save".
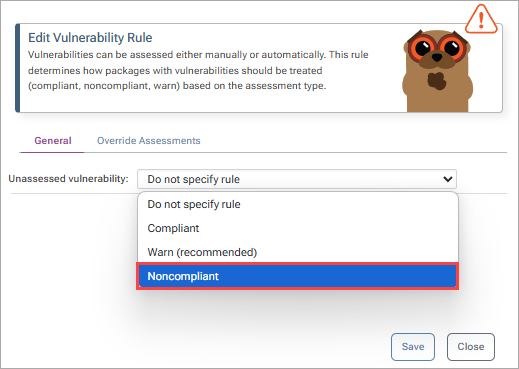
Now the compliance rules have been configured, any packages that are assessed to have unassessed vulnerabilities will be categorized as "Blocked" and will not be downloaded, with any attempt to download the package from the API resulting in a "404" error.
Step 7: (Optional) Add Custom Assessment Types
You can customize assessment types in ProGet to better reflect how your organization evaluates and responds to vulnerabilities. This is especially useful when default assessments don’t align with your workflows, risk tolerance, or the way your teams manage and prioritize remediation.
To edit or create your own assessment types, navigate to "Administration Overview" > "Vulnerabilities & Assessment Types" under "Global Components".
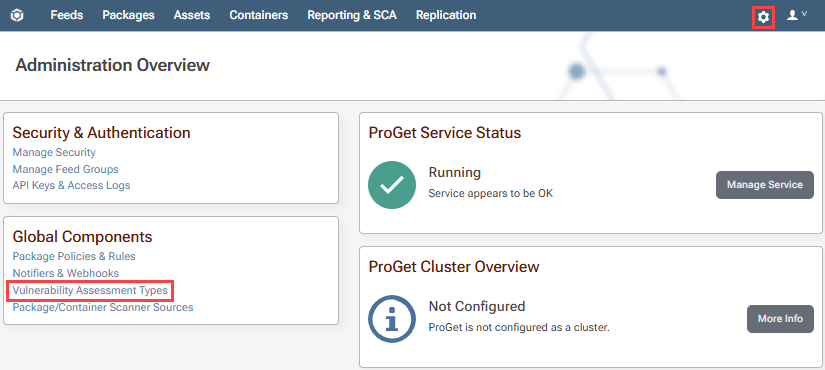
From here you can create an assessment type by clicking "Create Custom Assessment Type". By default, the assessment types of "Monitor", "Remediate", and "Contain" will be presented and automated.
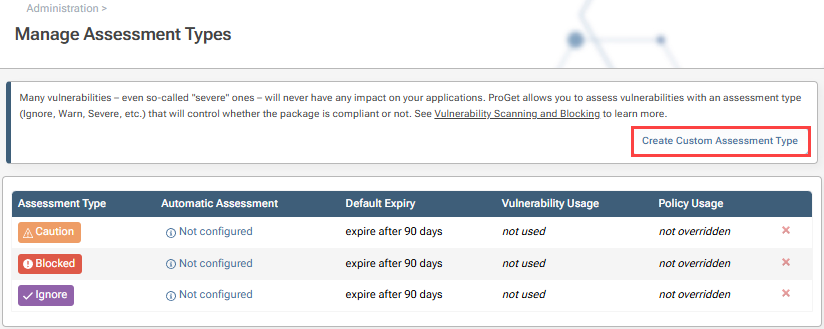
Auto assessment can be customized to your preferences. However, if you’re unsure of what the best option is; we recommend reading our page on Vulnerability Scanning & Blocking.
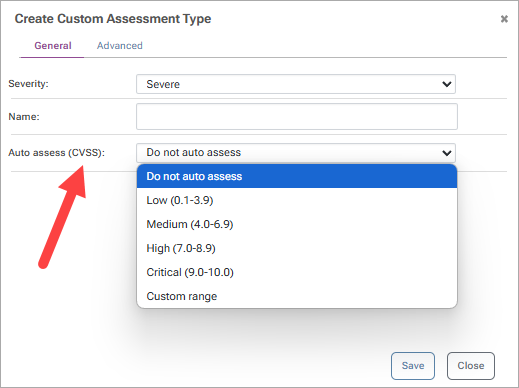
Once you have entered the details of your Assessment Type, click "Save".
Step 8: (Optional) Scan Container Vulnerabilities
To scan containers for vulnerabilities, ProGet extracts and inspects the files within each container image layer and looks for vulnerable packages that are installed. The "Packages" and "Vulnerabilities" tab of a container image will show these:

ProGet 2023 and Earlier
ProGet 2024 & 2025
Vulnerabilities had an overhaul in ProGet 2024. This was available as a preview feature in ProGet 2023.29+, which could be enabled by navigating to "Reporting & SCA" > "Vulnerabilities" and selecting "Enable Vulnerabilities Feature Preview...". To see how to scan and block packages in ProGet 2024 and 2025 see HOWTO: Scan and Block Packages in ProGet 2024 & 2025 (archive.org).
ProGet 2023 and Earlier
To see how to scan and block packages in earlier versions of ProGet 2023, see HOWTO: Scan and Block Packages in ProGet 2023 (archive.org).
In this article
- Step 1: Enable Vulnerabilities Feed Feature
- Step 2: Use Vulnerable Package
- Step 3: Scan your Build
- Step 4: (Optional) Run an audit
- Step 5: (Optional) Block Noncompliant Packages
- Step 6: (Optional) Edit Package Policy Rules
- Step 7: (Optional) Add Custom Assessment Types
- Step 8: (Optional) Scan Container Vulnerabilities
- ProGet 2023 and Earlier

